Products
Inspiration
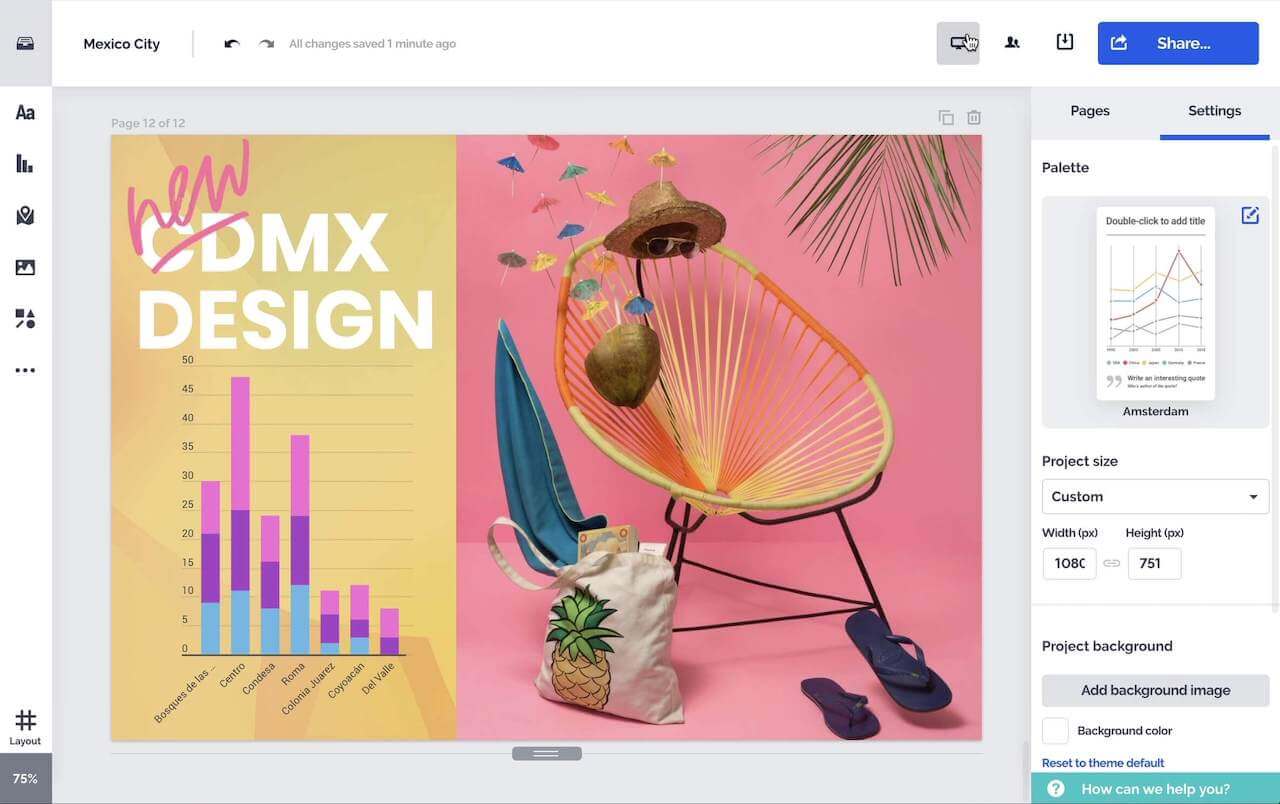
Recommended videos See how other users use Prezi Video to engage their audiences. Reusable presentations Browse some of our favorite presentations and copy them to use as templates. Reusable infographics Customize the content in these infographics to create your own works of art. Presentation templates Get a big head start when creating your own videos, presentations, or infographics.Solutions
Resources